Digital Signatures
Digital Signatures : A digital signature is used to authenticate the identity of the sender to the receiver to a limited extent in order to
Come and explore with me
 AI Agents with Memory Part 6: Multi-Agent Memory Sharing – Shared Memory Spaces Across Agent Networks with Redis and PostgreSQL
AI Agents with Memory Part 6: Multi-Agent Memory Sharing – Shared Memory Spaces Across Agent Networks with Redis and PostgreSQL
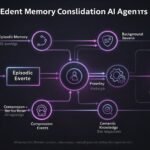 AI Agents with Memory Part 5: Memory Consolidation – Summarising and Compressing Long-Term History with Node.js Background Workers
AI Agents with Memory Part 5: Memory Consolidation – Summarising and Compressing Long-Term History with Node.js Background Workers
 Code in April 2026: Agentic Developers, the React Compiler Standard, and Rust Goes Mainstream
Code in April 2026: Agentic Developers, the React Compiler Standard, and Rust Goes Mainstream
 AI Agents with Memory Part 4: Procedural Memory – Agents That Learn From Past Actions Using C#
AI Agents with Memory Part 4: Procedural Memory – Agents That Learn From Past Actions Using C#
 The April 2026 AI Report: Model Wars, a 100x Energy Breakthrough, and the EU AI Act Countdown
The April 2026 AI Report: Model Wars, a 100x Energy Breakthrough, and the EU AI Act Countdown
 AI Agents with Memory Part 3: Semantic Memory – Building a Long-Term Knowledge Layer with Qdrant and Python
AI Agents with Memory Part 3: Semantic Memory – Building a Long-Term Knowledge Layer with Qdrant and Python
 The April 2026 Enterprise IT Report: IBM Bets on Arm, Wireless Networks Face a Security Crisis, and Hybrid Cloud Locks In as Standard
The April 2026 Enterprise IT Report: IBM Bets on Arm, Wireless Networks Face a Security Crisis, and Hybrid Cloud Locks In as Standard
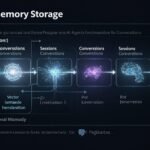 AI Agents with Memory Part 2: Episodic Memory – Storing and Retrieving Conversation History at Scale with PostgreSQL, pgvector, and Node.js
AI Agents with Memory Part 2: Episodic Memory – Storing and Retrieving Conversation History at Scale with PostgreSQL, pgvector, and Node.js
 AI Agents with Memory: Why Single-Session Agents Fail in Enterprise and the Three Memory Types That Fix It
AI Agents with Memory: Why Single-Session Agents Fail in Enterprise and the Three Memory Types That Fix It Digital Signatures : A digital signature is used to authenticate the identity of the sender to the receiver to a limited extent in order to
Basically, Steganography means of transmitting the message by hiding in any file like pictures, music, movies, or any file without changing the original file format.
Do you think “Why is it important?” The answer is yes it is very important because to catch a thief you must think like thief.
Cryptographic Algorithm Symmetric key Data Encryption Standard ( DES ) International Data Encryption Algorithm ( IDEA ) Rjindael (AES Standard ) Skipjack (used in ciphership
Some terms related to cryptography : Cryptography : It is the study of the mathematics techniques for all aspects of the information security. Cryptanalysis is
BIOS : Bios is a term that stands for the Basic Input / Output System. It consists of the low-level software that controls the system
File infector virus: Most common form of the computer virus is the file infector virus, that hides its code within the code of the another
Its the prank program that makes no effect with the computer hardware and software. It is just the irritating program that irritates the computer by