A comprehensive look at the biggest AI stories of April 2026: the model leaderboard reshuffle driven by Claude Opus 4.6 and Gemini 3.1 Ultra, a 100x energy efficiency breakthrough from Tufts University using neuro-symbolic AI, the August 2026 EU AI Act compliance deadline bearing down on enterprises, and major infrastructure bets from Anthropic, Snowflake, and Microsoft.
Tag: Compliance
AI Governance and Risk Management: Compliance Frameworks for Production Deployment
As AI systems transition from experimental pilots to production deployment, governance and risk management have become critical differentiators between organizations that scale successfully and those
Security and Compliance for Azure AI Foundry Agents: RBAC, Data Protection, and Regulatory Frameworks (Part 7 of 8)
Enterprise agentic AI deployments must meet rigorous security and compliance requirements protecting sensitive data, ensuring regulatory adherence, and maintaining organizational governance standards. This article provides
Monitoring, Observability and Governance Frameworks for Enterprise AI Agents
Establish governance frameworks for autonomous AI agents with regulatory compliance, runtime monitoring, and audit trails. Comprehensive guide covering EU AI Act, NIST AI RMF, ISO 42001, continuous oversight platforms, and enterprise governance strategies.
Complete Guide to Claude Agent Skills: Part 6 – Security Best Practices for Production
Master security for Claude Agent Skills with comprehensive threat modeling, automated security scanning, sandboxing strategies, credential management, network controls, and incident response. Includes production-ready Python code for skill auditing and compliance frameworks for GDPR, HIPAA, and SOC 2.
Model Context Protocol Part 4: Enterprise Integration Patterns – Security, Scaling, and Production Deployment
Master enterprise MCP integration with OAuth 2.1 authentication, role-based access control, monitoring, scaling, and security best practices. Production-ready patterns for deploying MCP servers at scale.
Azure AI Foundry Deep Dive Series Part 6: Security and Governance Implementation
Master security and governance for Azure AI Foundry. Learn network isolation patterns, identity management, data encryption, content safety, compliance frameworks, and incident response strategies for production AI systems.
Security-First Development: How Copilot Agent Catches Vulnerabilities Before Deployment
Conclude the series by exploring security-first development. Learn how Copilot agent catches vulnerabilities before deployment through multi-layered analysis, OWASP compliance, and proactive threat prevention.
Mastering Dead Letter Handling and Retry Policies in Azure Event Grid – Part 4: Advanced Topics and Reference Architecture
Welcome to the final part of our comprehensive Azure Event Grid resilience series! In Part 1, we covered foundational concepts, Part 2 explored implementation details,
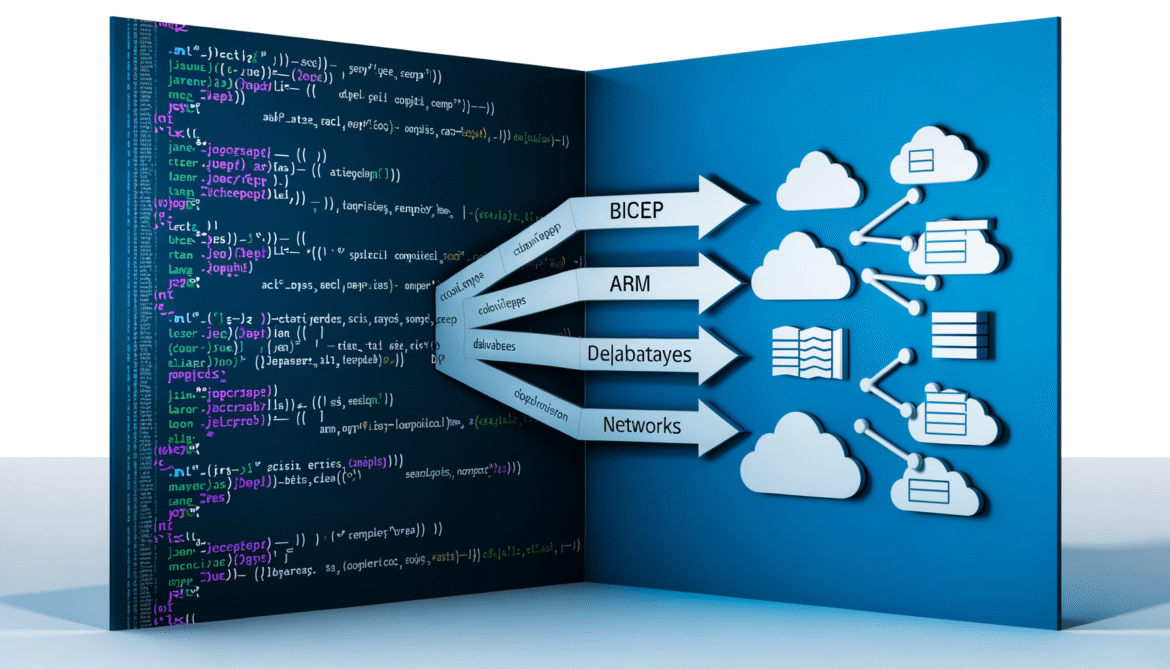
Infrastructure as Code with ARM Templates and Bicep: Part 7 – Enterprise Governance and Compliance
Enterprise Infrastructure as Code requires robust governance, compliance automation, and cost management. This final part covers Azure Policy integration, compliance frameworks, automated cost optimization, and